Was Your Account Affected By The Facebook Hack In September? Here's How You Can Check
30 million users were affected in the incident.
Late September, some 50 million Facebook users around the world were logged out of their accounts in what was later revealed to be a massive data breach
Facebook vice president of product management Guy Rosen was quick to address the problem in a blog post, where he claimed that "immediate action" had been taken to protect users' security.
"[I]t's clear that attackers exploited a vulnerability in Facebook's code that impacted 'View As', a feature that lets people see what their own profile looks like to someone else. This allowed them to steal Facebook access tokens which they could then use to take over people's accounts."
"Access tokens" are what keeps users logged in to their accounts, so they do not need to sign in each time they want to use Facebook.
More than two weeks later, Facebook revealed that 30 million accounts were affected in the "security incident"
The latest update was made through another blog post that went up on 12 October.
In the post, Rosen also explained how the attack was carried out. The TL;DR version is that an automated technique basically used the "snowball effect" to steal access tokens.
The attackers already had access to a set of accounts, allowing them to steal access tokens from users who are "friends" with the affected accounts - and on it goes.
Attackers have been able to access various bits of information for the 30 million users
Here's the breakdown:
- name and contact details of 15 million people,
- name, contact details, and other details such as hometown, current city, device types used to access Facebook, and tags of 14 million people,
- while one million people did not have their information accessed by the attackers.
New York Times technology reporter Mike Isaac, who was affected by the attack, shared screenshots showing the "wealth of personal information" that attackers have access to following the incident:
Here is how you can check if your account was affected by the hack:
Step 1 - Head to the Help Centre.
Step 2 - Scroll down the page until you come to a box with "Is my Facebook account impacted by this security issue?" as the title.
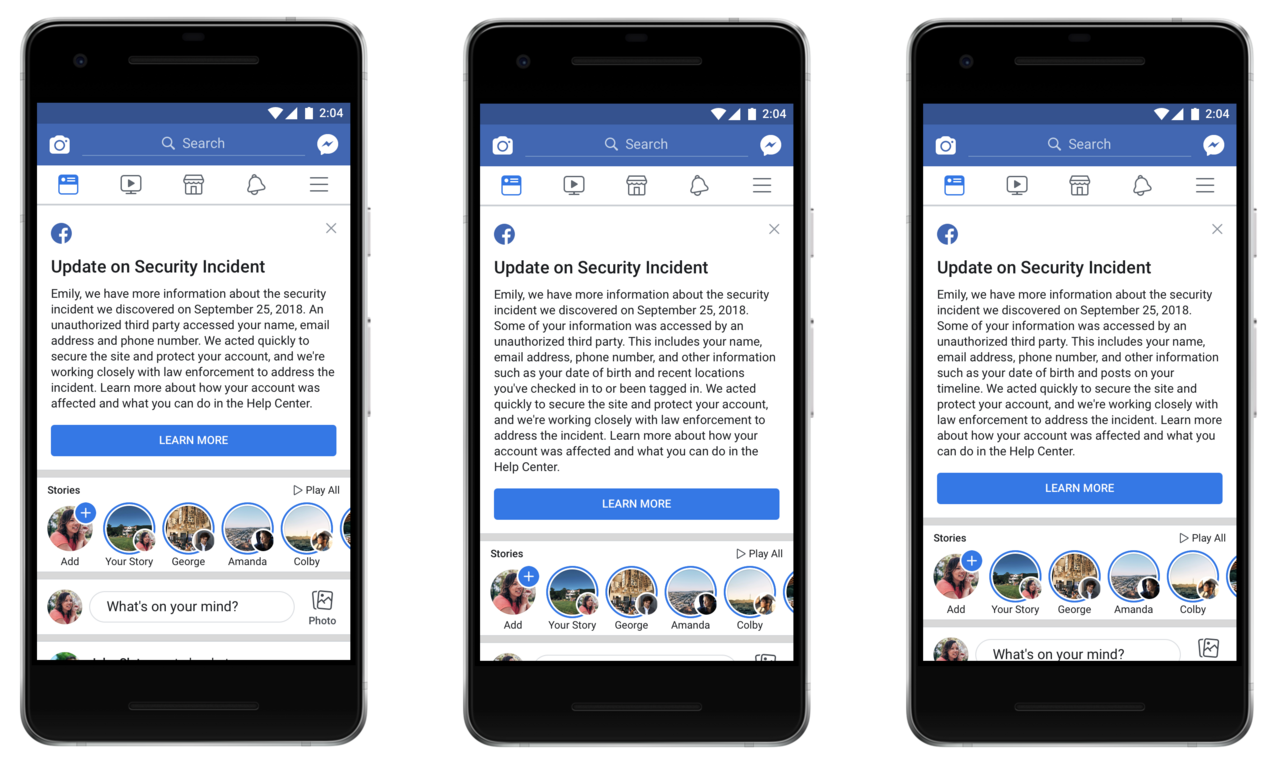
Facebook will also be sending customised messages to the 30 million affected users
The message will detail what information might have been accessed and what users can do to protect themselves against any suspicious emails, text messages, or calls.
"People's accounts have already been secured by the action we took two weeks ago to reset the access tokens for people who were potentially exposed - no one needs to log out again, and no one needs to change their password," Rosen said, according to Wired.
Rosen has also clarified that Messenger, Messenger Kids, Instagram, WhatsApp, Oculus, Workplace, Pages, payments, third-party apps, or advertising or developer accounts were not affected in the incident.