A New Ransomware Is Spreading Worldwide. Here's How To Protect Yourself From It
It is known as 'Petya'.
A new ransomware hit Ukraine on Tuesday, 27 June, and it has quickly spread across the world overnight
It is believed that the attack was first seeded through a software update mechanism on the Ukrainian government and business computer systems.
According to media reports, this outbreak is the biggest in Ukraine's history, and it has affected the government, banks, state power utilities, and Kiev’s airport and metro system.
The cyber attacks have since affected multiple global entities and caused major disruptions in Europe, the US, Australia and even parts of Asia.
The Tasmanian Cadbury chocolate factory in Australia, Danish shipping giant Maersk, and British advertising giant WPP are just some of the largest firms in the world that were reportedly affected by the ransomware.
What is Petya ransomware and how does it work?
Petya has been spreading rapidly through networks that use the Microsoft Windows system.
It was learned that Petya was first discovered in 2016, but some researchers opined that the current attack now appears to be a Petya offshoot, thus calling it 'NotPetya' or 'GoldenEye' instead.
Emsisoft CTO and Malware Researcher Fabian Wosar told Wired that Petya uses the same hacking tool in the WannaCry ransomware, namely 'EternalBlue', to spread the virus by exploiting the vulnerability in the Windows operating system.
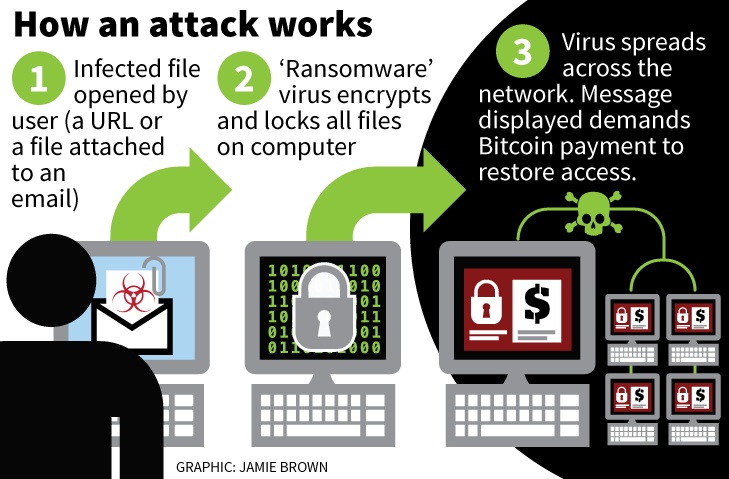
Once a computer is infected, the ransomware encrypts important documents and files, blocking access to all data. It the demands money, typically in Bitcoin, to restore access.
Although most reports are centred on how the ransomware has affected big businesses worlwide so far, it appears that consumers should also be cautious of the threats posed by this ransomware.
"Consumers are also at risk and should be wary if they are running operating systems that are vulnerable to the exploit, in other words if you have not patched," Raj Samani, chief scientist and fellow at McAfee reportedly said.
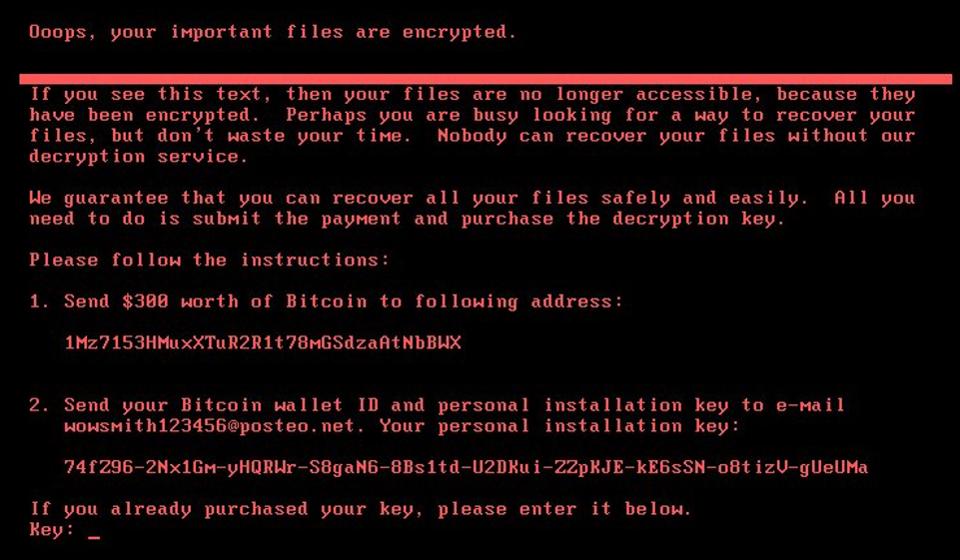
Users affected by the Petya ransomware are being told to pay USD300 (RM1,284.75) in Bitcoin
All Petya victims were instructed to direct the USD300 payment to the same single Bitcoin wallet ID. Then, they were told to send their own Bitcoin wallet ID and their respective personal installation key to a single email address in order to regain access to their data.
However, the email account that is being used to manage ransom demands has been blocked by the German email provider, Posteo.
About 36 victims have obliged and paid the ransom and the numbers are expected to keep growing, according to Blockchain.info, a website which shows Bitcoin transaction data.
It is still unclear about who might be behind the worldwide disruption, but experts have warned against paying the ransom since there is currently little chance that the files can be recovered.
Here's what you should do to protect yourself against the Petya ransomware:
1. Ensure that your computer systems have the latest patches or most recent security updates.
2. Backup your data regularly and keep a recent backup in another location, like an external hard drive or in the cloud. Choose to encrypt your own backup copy to ensure maximum security, in case it falls into the wrong hands.
3. Exercise caution when you encounter any unknown files or links. Don't click on anything suspicious and avoid opening attachments from recipients you don't know.
4. Install and use protection programs such as firewalls and anti-virus programme. Such programmes will alert you of any potential threats.